Elliptic curves over finite fields are powerful tools in cryptography and coding theory. They provide a discrete algebraic structure that enables secure encryption and efficient error correction. Understanding their properties and arithmetic is crucial for implementing robust cryptographic systems and error-correcting codes.
Linear error-correcting codes add redundancy to data, allowing detection and correction of transmission errors. These codes, including Hamming and Goppa codes, use mathematical structures to achieve optimal error-correcting capabilities. Their applications span telecommunications, data storage, and cryptography.
Elliptic curves over finite fields
- Elliptic curves over finite fields play a fundamental role in cryptography and coding theory
- Finite fields provide a discrete and bounded algebraic structure for defining elliptic curves
- Understanding the properties and arithmetic of elliptic curves over finite fields is crucial for their applications
Definitions and examples
- An elliptic curve over a finite field is defined by an equation of the form where and the discriminant
- The set of points satisfying the equation along with a special point at infinity denoted form the elliptic curve
- Example: The curve over the field consists of the points
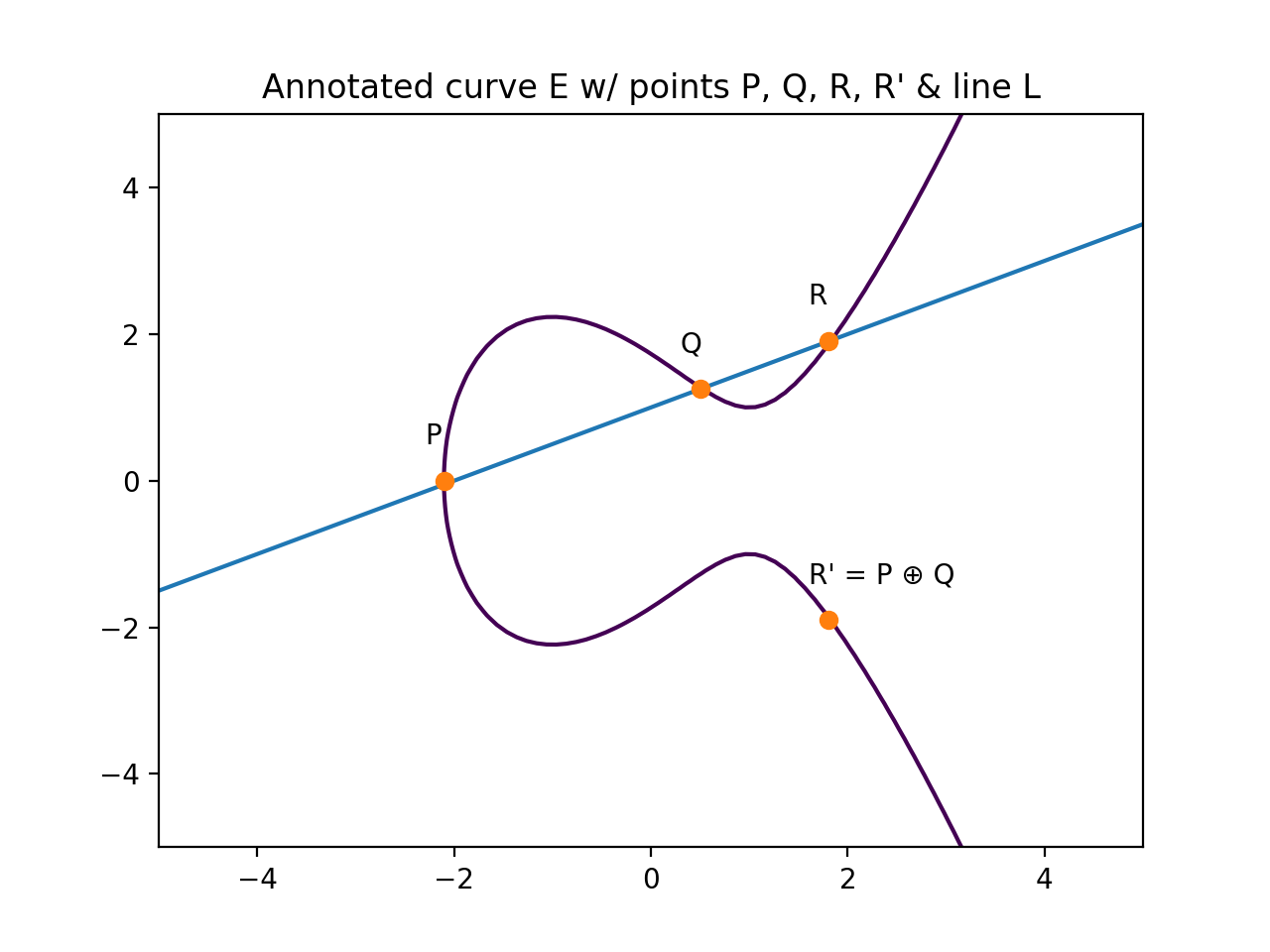
Group law and point addition
- The set of points on an elliptic curve over a finite field forms an abelian group under a well-defined addition operation
- The group law is based on the chord-and-tangent method for adding points geometrically
- Given two points and on the curve, their sum is defined as the reflection across the x-axis of the third point of intersection of the line through and with the curve
- The point at infinity serves as the identity element of the group
- Example: On the curve over , the sum of points and is
Finite field arithmetic
- Elliptic curve operations involve arithmetic in the underlying finite field
- Finite field elements are represented as integers modulo the field size
- Addition, subtraction, multiplication, and division in the finite field are performed modulo
- Efficient algorithms exist for finite field arithmetic, such as Montgomery multiplication and fast modular reduction techniques
- Example: In , the sum of and is (since ), and the product of and is (since )
Singular vs non-singular curves
- A non-singular elliptic curve over a finite field has a non-zero discriminant and forms a smooth curve without any cusps or self-intersections
- Singular curves have a vanishing discriminant and possess singularities or points of self-intersection
- Cryptographic applications typically use non-singular curves to ensure desirable group properties and security
- Example: The curve over is singular at the point , while the curve is non-singular
Linear error-correcting codes
- Linear error-correcting codes are mathematical constructions used for detecting and correcting errors in data transmission or storage
- They provide a systematic way to add redundancy to information symbols to enable error correction
- Linear codes are widely used in various applications, including telecommunications, data storage, and cryptography
Generator and parity check matrices
- A linear code of length and dimension over a finite field is a -dimensional subspace of the vector space
- The generator matrix is a matrix whose rows form a basis for the code
- The parity check matrix is an matrix such that , where denotes the transpose of
- Codewords in are obtained by multiplying a message vector with the generator matrix , i.e.,
- Example: The generator matrix over generates a linear code
Hamming codes and perfect codes
- Hamming codes are a family of linear codes with parameters for any positive integer
- They are single-error-correcting codes, capable of correcting any single-bit error in a codeword
- Perfect codes are codes that achieve the Hamming bound, meaning they have the maximum possible minimum distance for a given code length and dimension
- Hamming codes are perfect codes for the case of single-error correction
- Example: The Hamming code can correct any single-bit error in a 7-bit codeword

Bounds on minimum distance
- The minimum distance of a linear code determines its error-correcting capability
- The Singleton bound states that for an linear code
- The Hamming bound provides an upper bound on the size of a code with a given minimum distance
- Codes meeting the Singleton bound are called maximum distance separable (MDS) codes
- Example: The Hamming code meets the Singleton bound and is an MDS code
Decoding algorithms for linear codes
- Decoding algorithms aim to correct errors in received codewords and recover the original message
- Syndrome decoding is a common technique that computes the syndrome of a received word and uses it to determine the error pattern
- Maximum likelihood decoding finds the codeword closest to the received word in terms of Hamming distance
- Algebraic decoding methods, such as the Berlekamp-Massey algorithm, use the algebraic structure of the code for efficient decoding
- Example: Syndrome decoding of the Hamming code can correct any single-bit error by comparing the syndrome with a pre-computed syndrome table
Goppa codes from algebraic curves
- Goppa codes are a class of linear error-correcting codes constructed from algebraic curves over finite fields
- They provide a geometric approach to coding theory and offer advantages over classical linear codes in terms of code parameters and decoding efficiency
- Goppa codes have found applications in cryptography, such as the McEliece cryptosystem, due to their resistance to certain cryptanalytic attacks
Goppa's construction from curves
- Goppa codes are constructed from a smooth, projective, absolutely irreducible algebraic curve over a finite field
- Given a set of distinct -rational points on and a divisor on with support disjoint from the , the Goppa code is defined as the image of the evaluation map from the Riemann-Roch space to
- The generator matrix of the Goppa code is constructed from the basis elements of evaluated at the points
- Example: The Hermitian curve over can be used to construct Goppa codes with good parameters
Parameters of Goppa codes
- The length of a Goppa code is determined by the number of -rational points used in the construction
- The dimension of the code is related to the dimension of the Riemann-Roch space and can be computed using the Riemann-Roch theorem
- The minimum distance of the code is lower bounded by the degree of the divisor used in the construction
- Example: A Goppa code constructed from the Hermitian curve over with and has parameters
Decoding Goppa codes
- Decoding Goppa codes involves finding the closest codeword to a received word in terms of Hamming distance
- Efficient decoding algorithms for Goppa codes exploit the algebraic structure of the code and the underlying curve
- The Patterson algorithm is a widely used decoding method for Goppa codes, which reduces the decoding problem to solving a key equation and finding roots of an error locator polynomial
- Example: The Patterson algorithm can decode up to errors in a Goppa code constructed from a divisor
Advantages vs classical linear codes
- Goppa codes often achieve better parameters (length, dimension, minimum distance) compared to classical linear codes of the same length
- The geometric structure of Goppa codes provides additional algebraic properties that can be exploited for efficient decoding
- Goppa codes have a higher error-correcting capability for a given code rate compared to classical linear codes
- The security of certain cryptographic schemes, such as the McEliece cryptosystem, relies on the difficulty of decoding random Goppa codes, which is believed to be a hard problem
Elliptic curve cryptography
- Elliptic curve cryptography (ECC) is a public-key cryptography approach based on the algebraic structure of elliptic curves over finite fields
- ECC provides high security with smaller key sizes compared to other public-key cryptosystems, such as RSA
- The security of ECC relies on the difficulty of solving the elliptic curve discrete logarithm problem (ECDLP)
Diffie-Hellman key exchange on curves
- The Diffie-Hellman key exchange protocol can be adapted to work on elliptic curves over finite fields
- Two parties, Alice and Bob, agree on a public elliptic curve over a finite field and a base point on the curve
- Alice chooses a secret integer and computes , while Bob chooses a secret integer and computes
- Alice and Bob exchange their computed points and over a public channel
- Both parties can then compute the shared secret point using their respective secret integers
- The shared secret can be used to derive a symmetric key for secure communication
- Example: Using the curve over with base point , Alice chooses and Bob chooses , resulting in the shared secret point
Elliptic curve digital signatures
- Elliptic curve digital signature algorithms (ECDSA) provide a way to create and verify digital signatures using elliptic curves
- The signer has a private key and a corresponding public key , where is a base point on the curve
- To sign a message , the signer chooses a random integer , computes and , where is the order of
- The signer then computes , where is a cryptographic hash function
- The signature is the pair
- To verify a signature, the verifier computes , , , and
- The signature is valid if
- Example: Using the curve over with base point and a private key , a message can be signed and verified using ECDSA
Security based on discrete log problem
- The security of elliptic curve cryptography relies on the difficulty of the elliptic curve discrete logarithm problem (ECDLP)
- Given an elliptic curve over a finite field , a base point on the curve, and a point on the curve, the ECDLP is to find an integer such that
- The best known algorithms for solving the ECDLP have exponential time complexity, making it infeasible for properly chosen curve parameters
- The hardness of the ECDLP ensures the security of elliptic curve cryptographic schemes
- Example: On the curve over , given points and , finding the integer such that is an instance of the ECDLP
Comparisons vs RSA cryptosystem
- Elliptic curve cryptography offers several advantages compared to the RSA cryptosystem
- ECC achieves the same level of security as RSA with significantly smaller key sizes, reducing storage and transmission requirements
- ECC is more computationally efficient than RSA, especially for higher security levels
- The absence of efficient quantum algorithms for the ECDLP makes ECC a candidate for post-quantum cryptography
- Example: A 256-bit elliptic curve key provides similar security to a 3072-bit RSA key, demonstrating the key size advantage of ECC
Elliptic curve primality proving
- Elliptic curve primality proving (ECPP) is a probabilistic algorithm for determining the primality of a given integer using elliptic curves
- ECPP is based on the properties of elliptic curves over finite fields and provides an efficient and practical method for primality testing
Goldwasser-Kilian algorithm
- The Goldwasser-Kilian algorithm is a foundational ECPP algorithm that laid the groundwork for subsequent improvements
- It relies on the fact that the order of an elliptic curve over a finite field is close to for most curves
- The algorithm starts by randomly selecting an elliptic curve over and a point on the curve
- It then computes the order of and checks if divides and if is a prime power
- If the conditions are satisfied, the algorithm recursively proves the primality of using the same process
- The recursion continues until a small enough prime is reached, at which point the primality of is established
- Example: To prove the primality of , the Goldwasser-Kilian algorithm may select the curve and the point , which has order , and then recursively prove the primality of
Atkin-Morain improvements
- The Atkin-Morain ECPP algorithm improves upon the Goldwasser-Kilian algorithm by using complex multiplication (CM) methods to construct elliptic curves with known group orders
- Instead of randomly selecting curves, the Atkin-Morain algorithm uses curves with CM by imaginary quadratic fields with small discriminants
- The use of CM curves ensures that the group order of the curve can be efficiently computed and eliminates the need for recursive primality testing
- The Atkin-Morain algorithm also employs various optimizations, such as the use of isogenies and the computation of Hilbert class polynomials, to speed up the primality proving process