Elliptic curve cryptography (ECC) is a powerful public-key cryptosystem based on the algebraic structure of elliptic curves over finite fields. It offers smaller key sizes and faster computations compared to traditional systems like RSA, making it ideal for resource-constrained environments.
ECC's security relies on the elliptic curve discrete logarithm problem, which is believed to be computationally infeasible to solve. This chapter covers the basics of elliptic curves, key exchange protocols, digital signatures, and practical applications of ECC in modern cryptography.
Basics of elliptic curve cryptography
- Elliptic curve cryptography (ECC) is a public-key cryptosystem based on the algebraic structure of elliptic curves over finite fields
- ECC relies on the difficulty of solving the elliptic curve discrete logarithm problem (ECDLP) for its security
- Elliptic curves used in cryptography are defined over finite fields, which are mathematical structures with a finite number of elements
Elliptic curves over finite fields
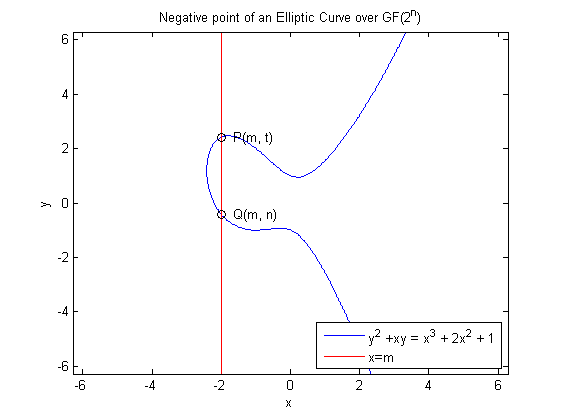
- An elliptic curve over a finite field is a set of points that satisfy a specific cubic equation, along with a special point called the "point at infinity"
- The most common finite fields used in ECC are prime fields and binary fields
- The choice of finite field affects the efficiency and security of the cryptographic operations performed on the elliptic curve
Elliptic curve equation
- The general form of an elliptic curve equation over a field is , where and the discriminant
- For cryptographic purposes, the elliptic curve equation is often simplified to for prime fields or for binary fields
- The coefficients and determine the shape of the elliptic curve and its cryptographic properties
Point addition and doubling
- Elliptic curves have a group structure under a point addition operation, which allows for the construction of cryptographic schemes
- Given two points and on an elliptic curve, their sum is defined as the point obtained by drawing a line through and and finding the third point of intersection with the curve
- Point doubling is a special case of point addition where , and the tangent line at is used to find the result of
- The formulas for point addition and doubling involve arithmetic operations in the underlying finite field
Cyclic subgroups and generators
- A cyclic subgroup of an elliptic curve is a subset of points that can be generated by repeatedly adding a specific point to itself
- The point used to generate the cyclic subgroup is called the generator or base point
- The order of a cyclic subgroup is the number of points in the subgroup, and the order of a point is the smallest positive integer such that (the point at infinity)
- Cryptographic protocols often rely on cyclic subgroups of prime order to ensure the security of the system
Elliptic curve discrete logarithm problem
- The security of elliptic curve cryptography relies on the difficulty of solving the elliptic curve discrete logarithm problem (ECDLP)
- The ECDLP is the foundation for various cryptographic schemes, such as key exchange and digital signatures
- Solving the ECDLP is believed to be computationally infeasible for properly chosen elliptic curves and key sizes
Computational intractability
- The ECDLP states that given an elliptic curve over a finite field, a point , and a point for some unknown integer , it is computationally infeasible to determine
- The best-known algorithms for solving the ECDLP have a running time that is exponential in the size of the underlying field
- The computational intractability of the ECDLP is what makes elliptic curve cryptography secure against attacks
Security of elliptic curve cryptography
- The security of ECC depends on the choice of the underlying finite field, the elliptic curve parameters, and the key size
- Cryptographically secure elliptic curves are chosen to resist known attacks, such as the Pollard's rho algorithm and the index calculus method
- Key sizes in ECC are typically smaller than those in other public-key cryptosystems (RSA) while providing the same level of security
Comparison vs integer factorization problem
- The integer factorization problem (IFP) is the basis for the security of the RSA cryptosystem
- The IFP involves finding the prime factors of a large composite number, which is believed to be computationally difficult
- For the same level of security, elliptic curve cryptography requires significantly smaller key sizes compared to RSA
- ECC is more efficient in terms of computational resources and bandwidth compared to cryptosystems based on the IFP
Elliptic curve key exchange
- Elliptic curve key exchange protocols allow two parties to establish a shared secret key over an insecure channel
- The shared secret key can be used for symmetric encryption, message authentication, or other cryptographic purposes
- Elliptic curve key exchange is based on the Diffie-Hellman key exchange protocol adapted to elliptic curves
Diffie-Hellman key exchange on elliptic curves
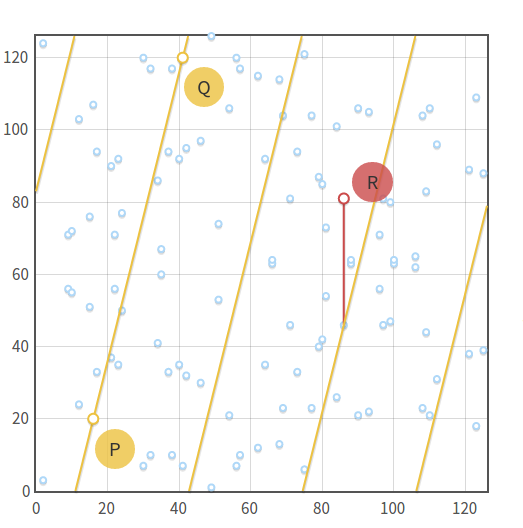
- The Diffie-Hellman key exchange protocol can be implemented using the group structure of elliptic curves
- Instead of using the multiplicative group of integers modulo a prime, the protocol uses the group of points on an elliptic curve
- The security of the elliptic curve Diffie-Hellman (ECDH) protocol relies on the difficulty of solving the ECDLP
Elliptic curve Diffie-Hellman (ECDH)
- In ECDH, the two parties agree on a common elliptic curve over a finite field, a base point of order , and a cryptographic hash function
- Each party generates a private key and (integers less than ) and computes their public keys and
- The parties exchange their public keys and compute the shared secret point
- The shared secret key is derived by hashing the x-coordinate of using the agreed-upon hash function
Key generation and exchange process
- Alice and Bob agree on the elliptic curve parameters
- Alice generates her private key and computes her public key
- Bob generates his private key and computes his public key
- Alice sends her public key to Bob, and Bob sends his public key to Alice
- Alice computes the shared secret point , and Bob computes the shared secret point
- Alice and Bob derive the shared secret key , where is the x-coordinate of
Shared secret derivation
- The shared secret point computed by both parties is the same, as
- To obtain the shared secret key, the x-coordinate of is hashed using the agreed-upon cryptographic hash function
- The hash function ensures that the shared secret key has a uniform distribution and a fixed length
- The resulting shared secret key can be used for symmetric encryption, message authentication, or key derivation for other purposes
Elliptic curve digital signature algorithm
- The Elliptic Curve Digital Signature Algorithm (ECDSA) is a variant of the Digital Signature Algorithm (DSA) that uses elliptic curve cryptography
- ECDSA is used for generating and verifying digital signatures, which provide authentication, integrity, and non-repudiation
- ECDSA signatures are more compact and computationally efficient compared to DSA signatures
ECDSA vs DSA
- ECDSA and DSA have similar signature generation and verification processes, but ECDSA uses elliptic curve operations instead of modular arithmetic
- ECDSA requires smaller key sizes than DSA for the same level of security, making it more suitable for resource-constrained environments
- ECDSA is based on the ECDLP, while DSA is based on the discrete logarithm problem in the multiplicative group of integers modulo a prime
Key generation and verification
- In ECDSA, the signer generates a key pair consisting of a private key (an integer less than the order of the base point) and a public key
- The public key is used for signature verification, while the private key is used for signature generation
- The verifier obtains the signer's public key through a trusted channel or a public key infrastructure (PKI)
Signature generation and verification process
-
Signature generation:
- The signer selects a random integer (less than ) and computes the point
- The signer calculates , where is the x-coordinate of
- The signer computes , where is the hash of the message
- The signature is the pair
-
Signature verification:
- The verifier computes and
- The verifier computes and the point
- The verifier calculates , where is the x-coordinate of
- The signature is valid if
Security and efficiency of ECDSA
- The security of ECDSA relies on the difficulty of solving the ECDLP and the collision resistance of the hash function used
- Properly implemented ECDSA with secure elliptic curve parameters and key sizes provides strong protection against forgery and tampering
- ECDSA is more efficient than DSA and RSA in terms of key sizes and computational costs, making it suitable for resource-constrained devices and high-volume signature applications
Elliptic curve cryptography in practice
- Elliptic curve cryptography has been widely adopted in various industry standards and protocols
- ECC is used in secure communication protocols, digital certificates, cryptocurrency systems, and embedded devices
- Standardized elliptic curves and domain parameters have been developed to ensure interoperability and security
Standardized elliptic curves
- Several organizations, such as NIST, SECG, and Brainpool, have published standardized elliptic curves for cryptographic use
- Examples of standardized curves include NIST P-256, secp256k1 (used in Bitcoin), and Curve25519 (used in Signal and WhatsApp)
- Standardized curves are chosen based on their security properties, efficiency, and resistance to known attacks
Curve parameters and domain parameters
- Elliptic curve domain parameters consist of the finite field, the elliptic curve equation, the base point, the order of the base point, and the cofactor
- Domain parameters are used to ensure that different implementations of ECC are interoperable and secure
- Curve parameters, such as the coefficients of the elliptic curve equation, are part of the domain parameters and determine the security and efficiency of the cryptographic operations
ECC in TLS and SSL
- Elliptic curve cryptography is used in the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols for secure web communication
- ECC cipher suites in TLS/SSL provide forward secrecy and improved performance compared to RSA-based cipher suites
- Examples of ECC cipher suites include ECDHE-ECDSA-AES256-GCM-SHA384 and ECDHE-RSA-AES128-GCM-SHA256
ECC in cryptocurrency and blockchain
- Elliptic curve cryptography is the foundation for many cryptocurrency systems and blockchain platforms
- Bitcoin and Ethereum use ECDSA with the secp256k1 curve for generating and verifying transaction signatures
- ECC enables compact and efficient signatures, which is crucial for scalability and performance in blockchain applications
Attacks on elliptic curve cryptography
- While elliptic curve cryptography is considered secure when properly implemented, various attacks have been proposed to exploit vulnerabilities in specific implementations or curve parameters
- Side-channel attacks and fault injection attacks target the physical implementation of ECC, while mathematical attacks aim to solve the ECDLP more efficiently
- Cryptographers and security researchers continuously study and improve ECC to mitigate the risk of attacks
Side-channel attacks
- Side-channel attacks exploit information leakage from the physical implementation of ECC, such as timing, power consumption, or electromagnetic emanations
- Examples of side-channel attacks include timing attacks, power analysis attacks, and cache attacks
- Countermeasures against side-channel attacks involve constant-time implementations, randomization techniques, and physical shielding
Fault injection attacks
- Fault injection attacks intentionally introduce errors into the computation of ECC operations to reveal sensitive information or bypass security checks
- Attackers may use techniques such as voltage glitches, laser pulses, or electromagnetic pulses to induce faults
- Countermeasures against fault injection attacks include error detection and correction, redundant computations, and physical tamper resistance
Pollard's rho algorithm
- Pollard's rho algorithm is a probabilistic method for solving the ECDLP in a cyclic subgroup of an elliptic curve
- The algorithm uses a pseudo-random walk on the elliptic curve to find a collision, which reveals the discrete logarithm
- The expected running time of Pollard's rho algorithm is , where is the order of the subgroup
- Selecting elliptic curves with a large prime order and implementing countermeasures like point blinding can mitigate the risk of Pollard's rho attack
Isogenies and supersingular curves
- Isogenies are mappings between elliptic curves that preserve the group structure
- Supersingular elliptic curves have a special structure that makes them vulnerable to attacks based on isogenies
- The supersingular isogeny Diffie-Hellman (SIDH) key exchange protocol, later known as SIKE, was proposed as a post-quantum cryptographic scheme
- However, recent research has shown that SIDH/SIKE is vulnerable to attacks and is no longer considered secure for post-quantum cryptography
Advantages and limitations of ECC
- Elliptic curve cryptography offers several advantages over other public-key cryptosystems, but it also has some limitations and challenges
- Understanding the strengths and weaknesses of ECC is essential for selecting the appropriate cryptographic scheme for a given application
- Ongoing research aims to improve the efficiency, security, and usability of ECC and address its limitations
Shorter key sizes vs RSA
- One of the main advantages of ECC is that it requires shorter key sizes compared to RSA for the same level of security
- For example, a 256-bit ECC key provides similar security to a 3072-bit RSA key
- Shorter key sizes result in reduced storage, transmission, and computation costs, making ECC suitable for resource-constrained environments
Computational efficiency
- ECC operations, such as point multiplication and addition, are computationally efficient compared to the modular exponentiation used in RSA
- The efficiency of ECC enables faster key generation, encryption, decryption, signing, and verification processes
- ECC is particularly advantageous for devices with limited processing power and battery life, such as smartphones, smart cards, and IoT devices
Implementation challenges
- Implementing ECC securely and efficiently requires careful attention to various aspects, such as curve selection, point representation, and side-channel protection
- ECC implementations must be thoroughly tested and validated to ensure they are free from vulnerabilities and conform to standards
- Interoperability between different ECC implementations can be challenging due to the variety of curve parameters and domain parameters in use
Future developments and research areas
- Research in elliptic curve cryptography continues to explore new techniques for improving efficiency, security, and functionality
- Areas of active research include post-quantum cryptography, pairing-based cryptography, and secure multiparty computation
- The development of quantum computers poses a threat to the security of ECC, as Shor's algorithm can solve the ECDLP in polynomial time
- Post-quantum cryptographic schemes based on other mathematical problems, such as lattices and isogenies, are being investigated as potential alternatives to ECC