IP Addressing and Subnetting
IP addressing forms the backbone of network communication, giving every device a unique numerical label so routers know where to send packets. Subnetting builds on this by letting you carve a single address block into smaller, right-sized pieces, which is essential for efficient network design, route summarization, and conserving limited address space.
IP Addressing
Structure of IP Addresses
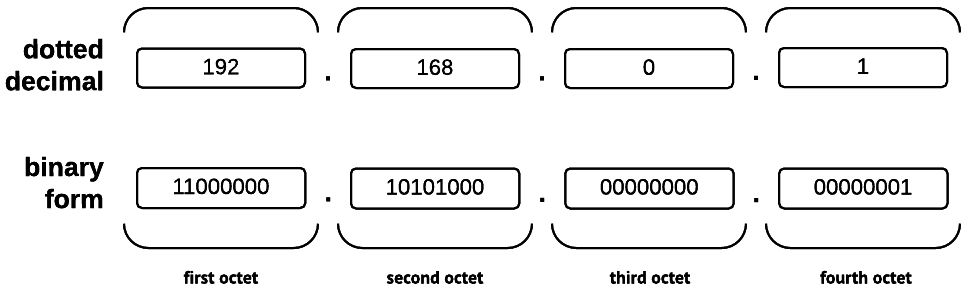
An IPv4 address is 32 bits long, written as four 8-bit octets in dotted-decimal notation (e.g., 192.168.1.1). Every address has two logical parts: a network portion that identifies which network the device belongs to, and a host portion that identifies the specific device on that network. The subnet mask is what draws the line between these two parts.
Classful address ranges (the legacy system you still need to know):
| Class | Range | Default Mask | Typical Use |
|---|---|---|---|
| A | 0.0.0.0 – 127.255.255.255 | 255.0.0.0 (/8) | Large networks |
| B | 128.0.0.0 – 191.255.255.255 | 255.255.0.0 (/16) | Medium networks |
| C | 192.0.0.0 – 223.255.255.255 | 255.255.255.0 (/24) | Small networks |
| D | 224.0.0.0 – 239.255.255.255 | N/A | Multicast |
| E | 240.0.0.0 – 255.255.255.255 | N/A | Reserved/experimental |
Classful addressing is mostly historical now. Modern networks use CIDR (covered below), which ignores class boundaries entirely. But understanding classes helps you recognize default masks and reason about legacy configurations.
IPv6 uses 128-bit addresses written as eight 16-bit groups (hextets) in hexadecimal, separated by colons:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
You can shorten IPv6 addresses by dropping leading zeros within each hextet and replacing one consecutive run of all-zero hextets with ::. The address above becomes 2001:db8:85a3::8a2e:370:7334. You can only use :: once per address, or the expansion becomes ambiguous.
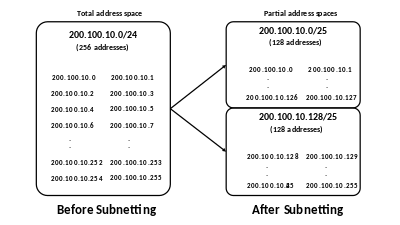
Subnetting Techniques for Networks
Subnetting means borrowing bits from the host portion and reassigning them to the network portion. This extends the subnet mask, creating more subnets with fewer hosts each.
How to subnet step by step:
- Determine requirements. How many subnets do you need? How many hosts per subnet?
- Calculate borrowed bits. Find the smallest such that gives you enough subnets.
- Build the new subnet mask. Take the original mask and set the next bits to 1. For example, borrowing 2 bits from a /24 gives you a /26 (subnet mask 255.255.255.192).
- Calculate subnet addresses. The "block size" (or increment) is where is the number of remaining host bits. For a /26, , so the block size is 64. Subnets start at .0, .64, .128, .192.
- Identify usable ranges. Within each subnet, the first address is the network address and the last is the broadcast address. Usable host addresses fall between them.
Variable Length Subnet Masking (VLSM) takes this further by allowing different subnets within the same network to have different prefix lengths. Instead of making every subnet the same size, you can give a 200-host LAN a /24 and a point-to-point link a /30. This avoids wasting addresses on small segments that only need a handful of hosts.
Subnetting Calculations and Design
Calculation of Hosts and Subnets
CIDR notation expresses an address and its mask compactly: 192.168.1.0/24 means the first 24 bits are the network portion. The /prefix number tells you exactly how many bits are set to 1 in the subnet mask.
The core formulas:
- Number of subnets = , where is the number of bits borrowed from the host portion
- Number of usable hosts per subnet = , where is the number of remaining host bits ( for IPv4). You subtract 2 because the network address (all host bits 0) and broadcast address (all host bits 1) can't be assigned to devices.
Quick example: A /26 has 6 host bits. That gives you usable hosts per subnet. If you started from a /24 and borrowed 2 bits, you created subnets.
To convert a subnet mask to CIDR, count the contiguous 1-bits. For 255.255.255.192, that's 11111111.11111111.11111111.11000000, which is 26 ones, so the prefix is /26.
Design of IP Addressing Schemes
Good IP addressing schemes don't happen by accident. A few design principles keep things manageable as networks grow:
- Hierarchical addressing assigns address blocks to regions, buildings, or departments in a structured way. This enables route summarization (also called supernetting or aggregation), where a single routing table entry can represent many subnets. Fewer entries means faster lookups and less memory usage on routers.
- Right-size your subnets with VLSM. Allocate based on actual need. A server VLAN with 50 hosts gets a /26; a WAN link between two routers only needs a /30 (2 usable addresses). Start by assigning the largest subnets first, then fill in smaller ones from the remaining space.
- Conserve public addresses. Use RFC 1918 private addresses (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16) for internal networks and deploy NAT (Network Address Translation) at the boundary to translate private addresses to public ones for internet-bound traffic.
- Document everything. Maintain an IP addressing plan that maps out the network hierarchy, subnet assignments, and address ranges. Consistent naming conventions for subnets and devices save significant troubleshooting time later. This sounds tedious, but a well-maintained address plan is the difference between a 5-minute fix and a 2-hour hunt.