Identity and access management is crucial for digital security in modern businesses. It ensures proper user authentication, protects sensitive data, and maintains regulatory compliance. Implementing robust practices safeguards against unauthorized access and potential data breaches.
Key components include identity repositories, authentication mechanisms, and authorization systems. The identity lifecycle involves user onboarding, ongoing management, and offboarding. Effective implementation balances security requirements with user productivity and convenience.
Fundamentals of identity management
- Identity management forms the cornerstone of digital security in modern businesses, ensuring proper user authentication and access control
- Effective identity management protects sensitive data, maintains regulatory compliance, and enhances overall cybersecurity posture
- Implementing robust identity management practices safeguards against unauthorized access and potential data breaches
Definition and purpose
- Process of creating, managing, and verifying digital identities within an organization
- Ensures authorized individuals access appropriate resources while preventing unauthorized entry
- Streamlines user experience by providing seamless access across multiple systems and applications
- Enhances security by enforcing consistent access policies and monitoring user activities
Key components
- Identity repository stores user information and credentials (Active Directory, LDAP)
- Authentication mechanisms verify user identities (passwords, biometrics, tokens)
- Authorization systems determine access rights based on user roles and permissions
- Provisioning and deprovisioning processes manage user account lifecycles
- Single sign-on (SSO) enables users to access multiple systems with one set of credentials
Identity lifecycle management
- User onboarding initiates the identity lifecycle, creating accounts and assigning initial access rights
- Ongoing management involves updating user information, modifying access privileges, and handling role changes
- Regular access reviews ensure users maintain appropriate permissions as their roles evolve
- Offboarding process revokes access rights and deactivates accounts when users leave the organization
- Automated workflows streamline lifecycle management, reducing administrative overhead and potential errors
Access control principles
- Access control principles form the foundation of secure identity and access management systems
- Implementing these principles helps organizations protect sensitive data and maintain regulatory compliance
- Effective access control balances security requirements with user productivity and convenience
Authentication vs authorization
- Authentication verifies the identity of users attempting to access a system or resource
- Involves validating credentials (usernames, passwords, biometrics) against stored information
- Authorization determines what actions or resources an authenticated user can access
- Based on user roles, permissions, and access policies defined by the organization
- Multi-factor authentication (MFA) enhances security by requiring multiple forms of verification
Least privilege principle
- Users granted minimum access rights necessary to perform their job functions
- Reduces potential damage from compromised accounts or insider threats
- Requires regular review and adjustment of user permissions as roles change
- Implements time-based access controls for temporary elevated privileges (just-in-time access)
- Supports compliance with data protection regulations (GDPR, HIPAA)
Role-based access control
- Access rights assigned based on predefined roles within the organization
- Simplifies access management by grouping users with similar job functions
- Enables consistent application of access policies across multiple users and systems
- Supports hierarchical structures with role inheritance for more granular control
- Facilitates auditing and compliance reporting by associating access rights with specific roles
Identity federation
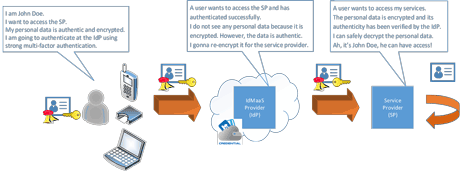
- Identity federation enables secure sharing of identity information across multiple organizations and systems
- Improves user experience by reducing the need for multiple login credentials
- Enhances security by centralizing identity management and enforcing consistent access policies
Single sign-on (SSO)
- Allows users to access multiple applications with a single set of credentials
- Reduces password fatigue and improves user productivity
- Enhances security by enforcing stronger authentication methods across all connected systems
- Supports both web-based and mobile applications through various protocols (SAML, OAuth)
- Simplifies access management and reduces IT support costs related to password resets
Identity providers
- Centralized services responsible for authenticating users and issuing identity assertions
- Can be internal (corporate directory) or external (social media platforms, government systems)
- Manage user credentials and authentication processes for multiple relying parties
- Support various authentication methods (passwords, biometrics, smart cards)
- Enable federation across organizations through trust relationships and standard protocols
Security Assertion Markup Language (SAML)
- XML-based open standard for exchanging authentication and authorization data
- Facilitates secure single sign-on across different domains and organizations
- Consists of three main components: identity provider, service provider, and user
- Supports web browser SSO profile for seamless user experience across web applications
- Enhances security by encrypting assertions and using digital signatures for integrity
Multifactor authentication
- Multifactor authentication significantly enhances security by requiring multiple forms of verification
- Helps prevent unauthorized access even if one factor (password) is compromised
- Balances security requirements with user experience to ensure adoption and effectiveness
Types of authentication factors
- Knowledge factors require information only the user knows (passwords, PINs, security questions)
- Possession factors involve physical items the user has (smart cards, mobile devices, hardware tokens)
- Inherence factors rely on unique biological characteristics (fingerprints, facial recognition, voice patterns)
- Location factors consider the user's physical or network location (GPS coordinates, IP addresses)
- Behavior factors analyze user actions and patterns (keystroke dynamics, mouse movements)
Benefits and challenges
- Significantly reduces the risk of unauthorized access and account takeovers
- Provides an additional layer of security against phishing attacks and credential stuffing
- May introduce friction in the user experience, potentially impacting productivity
- Requires careful implementation to balance security with usability and convenience
- Increases costs associated with deploying and maintaining additional authentication infrastructure
Implementation strategies
- Risk-based authentication applies MFA selectively based on contextual factors (location, device, activity)
- Adaptive authentication adjusts security requirements in real-time based on user behavior and risk levels
- Push notifications to mobile devices offer a user-friendly alternative to traditional one-time passwords
- Biometric authentication leverages smartphone capabilities for convenient and secure verification
- Integration with single sign-on systems streamlines the MFA process across multiple applications
Identity governance
- Identity governance ensures proper management and control of user identities and access rights
- Helps organizations maintain compliance with regulatory requirements and internal policies
- Reduces security risks by enforcing consistent access controls and monitoring user activities
Policy management
- Defines and enforces access policies across the organization's systems and applications
- Implements role-based access control (RBAC) to align access rights with job functions
- Establishes approval workflows for access requests and privilege escalations
- Automates policy enforcement to ensure consistent application of security controls
- Supports dynamic policy adjustments based on user context and risk factors
Compliance and auditing
- Monitors user activities and access patterns to detect potential security violations
- Generates comprehensive audit trails for regulatory compliance (SOX, HIPAA, GDPR)
- Conducts regular access reviews to identify and remediate inappropriate permissions
- Implements segregation of duties to prevent conflicts of interest and reduce fraud risks
- Provides reporting capabilities for demonstrating compliance during audits and assessments
Risk assessment
- Evaluates potential security risks associated with user access and permissions
- Identifies high-risk users and privileged accounts requiring additional monitoring
- Assesses the impact of granting or revoking access rights on business operations
- Implements continuous monitoring to detect anomalous behavior and potential threats
- Integrates with security information and event management (SIEM) systems for holistic risk analysis
Biometric authentication
- Biometric authentication leverages unique physical or behavioral characteristics for user verification
- Offers enhanced security and convenience compared to traditional password-based systems
- Raises important privacy and ethical considerations in the collection and storage of biometric data
Types of biometric identifiers
- Physiological biometrics include fingerprints, facial features, iris patterns, and hand geometry
- Behavioral biometrics analyze unique patterns in voice, signature, gait, and keystroke dynamics
- Emerging technologies explore DNA matching, ear shape recognition, and vein pattern analysis
- Multimodal biometrics combine multiple identifiers for increased accuracy and security
- Contactless biometrics (facial recognition, iris scanning) gain popularity in hygiene-conscious environments
Accuracy and reliability
- Measured by false acceptance rate (FAR) and false rejection rate (FRR) of the biometric system
- Environmental factors (lighting, background noise) can impact the accuracy of certain biometrics
- Liveness detection prevents spoofing attempts using photos, recordings, or artificial replicas
- Continuous authentication monitors biometric patterns throughout a session for ongoing verification
- Machine learning algorithms improve accuracy and adapt to changes in biometric characteristics over time
Privacy concerns
- Collection and storage of biometric data raise significant privacy and data protection issues
- Biometric information considered sensitive personal data under regulations like GDPR
- Potential for unauthorized access or misuse of biometric data poses serious security risks
- Concerns about government surveillance and tracking using biometric identifiers
- Ethical considerations regarding consent and the right to anonymity in public spaces
Identity as a Service (IDaaS)
- Identity as a Service provides cloud-based identity and access management solutions
- Offers scalable and flexible IAM capabilities for organizations of all sizes
- Enables businesses to focus on core operations while leveraging expert-managed identity services
Cloud-based identity management
- Centralizes identity and access management functions in a cloud-hosted platform
- Supports user authentication, authorization, and single sign-on across multiple applications
- Provides directory services and user provisioning capabilities for cloud and on-premises systems
- Offers API-based integration with various enterprise applications and services
- Enables adaptive and risk-based authentication for enhanced security
Benefits for businesses
- Reduces infrastructure costs and management overhead associated with on-premises IAM systems
- Improves scalability and flexibility to accommodate changing business needs and user populations
- Enhances security through regular updates, patches, and expert management of identity services
- Facilitates rapid deployment and integration of new applications and services
- Supports remote work and bring-your-own-device (BYOD) policies with secure access from anywhere

Security considerations
- Data residency and sovereignty concerns when storing identity information in the cloud
- Potential for service disruptions or outages impacting access to critical business applications
- Importance of strong encryption and access controls to protect sensitive identity data
- Need for careful vendor selection and thorough security assessments of IDaaS providers
- Compliance requirements for handling and storing identity information in cloud environments
Zero Trust security model
- Zero Trust challenges traditional perimeter-based security approaches in modern digital environments
- Assumes no implicit trust, requiring continuous verification of users, devices, and network segments
- Integrates closely with identity and access management to enforce granular access controls
Principles of Zero Trust
- Verify explicitly authenticates and authorizes every access request regardless of source
- Use least privilege access granting minimum necessary rights for the specific task or role
- Assume breach mentality treats all network traffic and access attempts as potentially malicious
- Implements micro-segmentation to isolate and protect individual workloads and data
- Enables continuous monitoring and real-time threat detection across the entire environment
Implementation challenges
- Requires significant changes to existing network architecture and security practices
- Demands comprehensive visibility into all users, devices, and network traffic
- Necessitates integration of multiple security technologies and tools for effective implementation
- May impact user experience and productivity if not carefully designed and optimized
- Involves cultural shifts in IT and security teams to embrace the Zero Trust mindset
Integration with IAM
- Leverages strong authentication methods, including multifactor authentication, for all access requests
- Implements fine-grained authorization policies based on user identity, device health, and context
- Utilizes continuous authentication to verify user identity throughout active sessions
- Integrates with identity governance for ongoing access reviews and policy enforcement
- Supports just-in-time (JIT) and just-enough-access (JEA) provisioning for privileged accounts
Ethical considerations
- Ethical considerations in identity and access management balance security needs with individual rights
- Address privacy concerns and data protection requirements in an increasingly connected world
- Ensure responsible and transparent use of personal information in digital identity systems
Privacy vs security
- Balances the need for robust security measures with individuals' right to privacy
- Implements data minimization principles to collect only necessary identity information
- Considers the potential impact of surveillance and monitoring on personal freedoms
- Addresses concerns about profiling and discrimination based on identity attributes
- Explores privacy-enhancing technologies (PETs) to achieve security goals while protecting privacy
Data protection regulations
- Compliance with GDPR, CCPA, and other data protection laws governing personal information
- Implements data subject rights (access, rectification, erasure) for identity-related information
- Ensures lawful basis for processing identity data, including obtaining informed consent
- Conducts data protection impact assessments (DPIAs) for high-risk identity management activities
- Establishes data retention policies and secure deletion procedures for identity information
Consent and transparency
- Provides clear and accessible information about identity data collection and use
- Obtains informed consent for collecting and processing biometric and other sensitive data
- Offers granular control over sharing of identity information with third parties
- Implements privacy dashboards for users to manage their identity and access preferences
- Ensures transparency in automated decision-making processes related to identity and access
Future trends in IAM
- Future trends in identity and access management focus on enhancing security, usability, and privacy
- Emerging technologies promise to revolutionize how digital identities are created, managed, and verified
- Innovations aim to address current IAM challenges while preparing for evolving threat landscapes
Artificial intelligence in IAM
- Machine learning algorithms detect anomalous behavior and potential account compromises
- AI-powered risk scoring enables more accurate and dynamic access decisions
- Natural language processing improves user interactions with IAM systems (chatbots, voice commands)
- Predictive analytics anticipate user needs and automate access provisioning processes
- Continuous authentication leverages AI to analyze behavioral biometrics throughout user sessions
Blockchain for identity management
- Decentralized identity systems built on blockchain technology enhance privacy and user control
- Self-sovereign identity allows individuals to own and manage their digital identities
- Immutable ledgers provide tamper-proof audit trails for identity transactions and verifications
- Smart contracts automate identity-related processes and enforce access policies
- Blockchain-based identity federation enables secure sharing of identity information across organizations
Decentralized identity systems
- User-centric approach gives individuals greater control over their digital identities
- Verifiable credentials enable secure and privacy-preserving sharing of identity attributes
- Decentralized identifiers (DIDs) provide globally unique and persistent identifiers for users
- Peer-to-peer authentication eliminates the need for centralized identity providers
- Integration with emerging standards (W3C Verifiable Credentials, DID) for interoperability