Privacy laws and regulations define how organizations must collect, use, store, and protect personal data. For network security professionals, understanding these laws is essential because a single compliance failure can trigger massive fines, legal action, and lasting reputational harm. This guide covers the major privacy laws at federal, state, and international levels, the core principles behind them, what compliance actually looks like in practice, and the consequences of getting it wrong.
Types of privacy laws
Privacy laws are regulations that govern how organizations and government entities handle personal information. These laws exist at multiple levels (federal, state, and international), and they often overlap. As a security professional, you need to know which laws apply to your organization based on the type of data you handle, where your users are located, and what industry you operate in.
Federal privacy laws
Federal privacy laws are enacted by the U.S. Congress and apply nationwide, creating a baseline level of protection for personal data. They tend to be sector-specific, meaning each law targets a particular industry:
- HIPAA protects healthcare data
- FERPA protects student education records
- GLBA protects personal financial information
These laws generally require organizations to implement specific security measures, obtain consent for data collection, and notify individuals when breaches occur. Enforcement falls to agencies like the Federal Trade Commission (FTC) and the Department of Health and Human Services (HHS), depending on the law.
State privacy laws
State privacy laws are enacted by individual state legislatures and often provide protections that go beyond federal requirements. Two prominent examples:
- The California Consumer Privacy Act (CCPA) gives California residents the right to know what data businesses collect, to delete that data, and to opt out of its sale.
- The New York SHIELD Act imposes stricter data security requirements on businesses that handle New Yorkers' private information.
State laws typically give individuals more direct control over their personal data. They're enforced by state attorneys general, who can bring legal action against violating organizations. If your organization operates across multiple states, you need to comply with each state's laws separately.
International privacy laws
International privacy laws govern data protection across countries and regions. The most significant is the EU's General Data Protection Regulation (GDPR), which sets strict rules for collecting, using, and transferring personal data of EU residents.
Other countries with notable privacy frameworks include Canada (PIPEDA), Australia (Privacy Act 1988), and Japan (APPI). A critical concept here is extraterritorial reach: these laws apply to your organization even if you're located outside the country, as long as you process data belonging to that country's residents. Non-compliance can result in substantial fines and legal consequences.
Key privacy regulations
These are the specific laws you're most likely to encounter on exams and in practice. Each targets a different type of data or industry.
HIPAA for healthcare data
The Health Insurance Portability and Accountability Act (HIPAA) sets national standards for protecting protected health information (PHI). It applies to covered entities (healthcare providers, health plans, healthcare clearinghouses) and their business associates (any third party that handles PHI on their behalf).
HIPAA has two main rules to know:
- The Privacy Rule governs how PHI can be used and disclosed. It requires patient consent, privacy practice notices, and limits on who can access PHI.
- The Security Rule requires administrative, physical, and technical safeguards to protect electronic PHI (ePHI). Think encryption, access controls, and audit logs.
Violations can result in civil and criminal penalties, with fines reaching up to per year for each violation category.
FERPA for student records
The Family Educational Rights and Privacy Act (FERPA) protects the privacy of student education records. It applies to all educational institutions receiving U.S. Department of Education funding, from K-12 schools through universities.
Key provisions:
- Parents (or eligible students over 18) have the right to access, review, and request corrections to education records.
- Institutions must obtain written consent before disclosing personally identifiable information from student records, with limited exceptions (e.g., school officials with a legitimate educational interest).
- The penalty for violations is the potential loss of federal funding, which makes compliance a high-stakes issue for schools.
GLBA for financial data
The Gramm-Leach-Bliley Act (GLBA) requires financial institutions to protect customers' personal financial information. It covers banks, credit unions, insurance companies, and other financial service providers.
Two rules to know:
- The Privacy Rule requires institutions to provide customers with privacy notices explaining data-sharing practices and give them the right to opt out of certain sharing.
- The Safeguards Rule mandates a comprehensive information security program to protect customer data from unauthorized access, use, or disclosure.
Violations can lead to civil penalties, regulatory enforcement actions, and significant reputational damage.
GDPR in the European Union
The General Data Protection Regulation (GDPR) is one of the most comprehensive privacy laws in the world. It applies to any organization processing personal data of EU residents, regardless of where that organization is located.
Key requirements:
- Individuals have rights to access, rectify, erase, and object to the processing of their personal data.
- Organizations must obtain explicit consent for data processing.
- Data breaches must be reported to authorities within 72 hours of discovery.
- Organizations must implement privacy by design, meaning data protection must be considered from the start of any product or system development.
Fines for non-compliance can reach up to €20 million or 4% of global annual revenue, whichever is higher. These are the largest privacy penalties in the world.
CCPA in California
The California Consumer Privacy Act (CCPA) gives California residents significant control over their personal data. It applies to businesses that meet at least one of these thresholds:
- Annual gross revenues over
- Buying, receiving, or selling personal information of 50,000 or more California residents
Under CCPA, individuals have the right to:
- Know what personal information is being collected about them
- Delete their data
- Opt out of the sale of their personal information
Businesses must provide clear privacy notices and respond to consumer requests within specific timeframes. Penalties can reach per intentional violation and per unintentional violation.
Principles of data privacy
These principles form the foundation of most privacy laws worldwide. Even when specific regulations differ, they almost always trace back to these core ideas.
Notice and consent
Organizations must inform individuals about their data practices and obtain consent before processing personal information. Privacy notices should be clear and accessible, explaining what data is collected, how it's used, and who it's shared with.
Consent must be freely given, specific, informed, and unambiguous. Individuals should be able to withdraw consent at any time. Organizations should also offer meaningful choices, like the ability to opt out of certain uses.
Purpose limitation
Personal data should only be collected and processed for specified, explicit, and legitimate purposes. You can't collect data for one reason and then use it for something completely different without getting additional consent. Organizations should clearly document why they're collecting data and make sure all subsequent processing stays aligned with those original purposes.
Data minimization
Collect only what you actually need. Organizations should limit the personal data they gather, store, and use to what's strictly necessary for their stated purposes. Hoarding unnecessary data increases breach risk. Regular reviews to identify and delete data that's no longer needed help maintain compliance.
Accuracy of data
Organizations must take reasonable steps to keep personal data accurate, complete, and up-to-date. Inaccurate data can lead to wrong decisions and real harm to individuals. This means verifying data at collection, giving individuals ways to review and correct their information, and performing regular data quality checks.
Storage limitation
Don't keep data longer than you need it. Organizations should establish data retention policies that define how long different types of data are stored based on legal, regulatory, and business requirements. Once data is no longer needed for its original purpose, it should be securely deleted or anonymized.
Security of processing
Organizations must implement appropriate technical and organizational measures to protect personal data from unauthorized access, alteration, disclosure, or destruction. This includes measures like encryption, access controls, network segmentation, monitoring, and employee training. Security measures should be regularly assessed and updated as threats evolve.
Accountability and auditing
Organizations must take responsibility for their data practices and be able to demonstrate compliance. This involves:
- Appointing a Data Protection Officer (DPO) or equivalent role
- Developing internal policies, procedures, and training programs
- Conducting regular audits and assessments
- Maintaining documentation of data processing activities, privacy impact assessments, and breach response plans
Compliance requirements
Compliance isn't just about knowing the laws. It requires concrete actions and ongoing effort. Here's what organizations actually need to have in place.
Privacy policies
A privacy policy is a written statement that tells individuals how an organization handles their data. It must be clear, comprehensive, and aligned with applicable laws. A solid privacy policy covers:
- What types of personal data are collected
- The purposes for which data is used
- Who data may be shared with
- What security measures protect the data
- What rights individuals have (access, correction, deletion)
- Contact information for privacy inquiries
Privacy policies must be easily accessible, regularly reviewed, and updated whenever data practices or legal requirements change.
Data protection measures
These are the technical and organizational safeguards that actually secure personal data. They should protect confidentiality, integrity, and availability throughout the data lifecycle. Common measures include:
- Technical: encryption, access controls, network segmentation, firewalls, intrusion detection systems
- Physical: secure data centers, locked filing cabinets, visitor management systems
All protection measures need regular assessment, testing, and updating to keep pace with evolving threats.
Breach notification procedures
When a data breach occurs, organizations must follow specific steps to notify affected individuals and relevant authorities. Most privacy laws specify timeframes and content requirements for these notifications.
Organizations should maintain a data breach response plan that covers:
- Containing the breach to prevent further data loss
- Assessing the scope and impact of the breach
- Notifying affected individuals and authorities within required timeframes
- Providing support and remediation to affected individuals
- Documenting the incident and lessons learned
Regular testing of this plan ensures the organization can respond effectively when a real breach happens.
Employee training programs
Even the best technical controls fail if employees don't understand privacy requirements. Training programs should cover data privacy principles, security best practices, incident reporting procedures, and the consequences of non-compliance.
Employees who handle sensitive data (HR, marketing, customer service) should receive role-specific training. Training should be conducted regularly and updated to reflect changes in laws or policies. Organizations should track completion and assess effectiveness through quizzes or other evaluations.
Third-party vendor management
When external vendors process personal data on your behalf, your organization is still responsible for protecting that data. Vendor management involves:
- Conducting due diligence before engaging a vendor to verify their privacy and security practices
- Including data privacy and security obligations in contracts (confidentiality agreements, security requirements, audit rights)
- Regularly monitoring vendor compliance with privacy laws and contractual terms
If a third-party vendor causes a breach or fails to comply, the hiring organization can still be held liable and face legal, financial, and reputational consequences.
Enforcement and penalties
Privacy laws have real teeth. Understanding the enforcement landscape helps you communicate the business case for privacy investments within your organization.
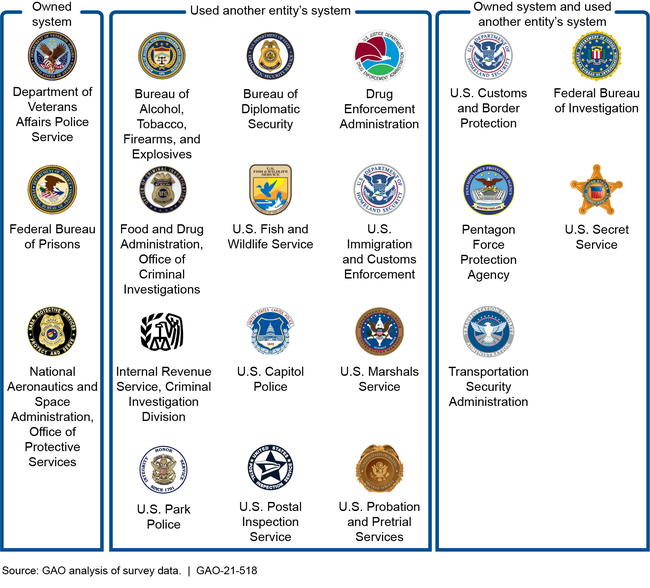
Federal enforcement agencies
Federal agencies investigate and enforce federal privacy laws. The key players include:
- Federal Trade Commission (FTC): Enforces against unfair or deceptive data practices
- Department of Health and Human Services (HHS): Enforces HIPAA
- Federal Communications Commission (FCC): Enforces telecommunications privacy rules
These agencies can conduct investigations, issue subpoenas, impose civil penalties, require corrective actions, and enter into consent decrees. They sometimes collaborate with state attorneys general or international authorities on enforcement.
State attorneys general
State attorneys general enforce state privacy laws and protect their residents' interests. Many state laws, like the CCPA, specifically grant enforcement authority to the state AG. They can conduct investigations, file lawsuits, and seek injunctions or civil penalties. Multi-state enforcement actions, where several AGs collaborate, are increasingly common. Organizations operating across multiple states must track each state's enforcement mechanisms.
Private rights of action
Some privacy laws allow individuals to sue organizations directly for violations. Notable examples include the Illinois Biometric Information Privacy Act (BIPA) and certain provisions of the CCPA. Individuals may seek monetary damages, injunctions, or other relief. Class action lawsuits, where groups of affected individuals sue collectively, are a common and financially significant form of private enforcement in privacy cases.
Civil and criminal penalties
- Civil penalties are imposed by enforcement agencies and include fines, injunctions, and corrective action requirements.
- Criminal penalties apply to severe or willful violations and can include fines and imprisonment for responsible individuals.
Penalty amounts vary by law and violation severity. For reference: GDPR fines can reach €20 million or 4% of global revenue, while CCPA fines go up to per intentional violation.
Reputational damage risks
Beyond formal penalties, privacy violations cause reputational harm that can be harder to recover from than the fines themselves. Breaches lead to negative media coverage, customer complaints, and loss of business. The financial impact includes lost revenue, increased customer churn, and decreased market share.
Organizations that handle incidents transparently and respond responsibly can mitigate some of this damage. Strong privacy practices and a well-tested incident response plan are the best defenses against reputational fallout.
Privacy by design
Privacy by design is a proactive approach that integrates privacy considerations into the design and development of products, services, and systems from the very beginning. Rather than treating privacy as a compliance checkbox after development is complete, this approach makes it a core component of how technology and business processes are built.
Proactive vs reactive approaches
A proactive approach means anticipating privacy risks before they materialize. You build protections into systems during the design phase, conduct privacy impact assessments early, and make data protection a default setting. A reactive approach, by contrast, means addressing privacy only after a problem occurs, such as patching vulnerabilities after a breach or updating policies only after a regulatory complaint.
Privacy by design favors the proactive model. The goal is to prevent privacy incidents rather than respond to them. This means security and privacy teams should be involved from the earliest stages of system design, not brought in at the end to review a finished product.