Hash functions are essential tools in network security and forensics, mapping arbitrary-length inputs to fixed-length outputs. They ensure data integrity, authentication, and non-repudiation through properties like deterministic output, fixed-length output, and resistance to various attacks.
Cryptographic hash functions come in different types, including MD5, SHA-1, and the more secure SHA-2 and SHA-3 families. These functions find applications in data integrity verification, password storage, digital signatures, and blockchain technology, playing a crucial role in modern security protocols.
Definition of hash functions
- Hash functions map arbitrary-length input data to fixed-length output values called hash values or digests
- Designed to be computationally efficient one-way functions that produce unique outputs for each input
- Play a crucial role in ensuring data integrity, authentication, and non-repudiation in network security and forensics applications
Properties of cryptographic hash functions
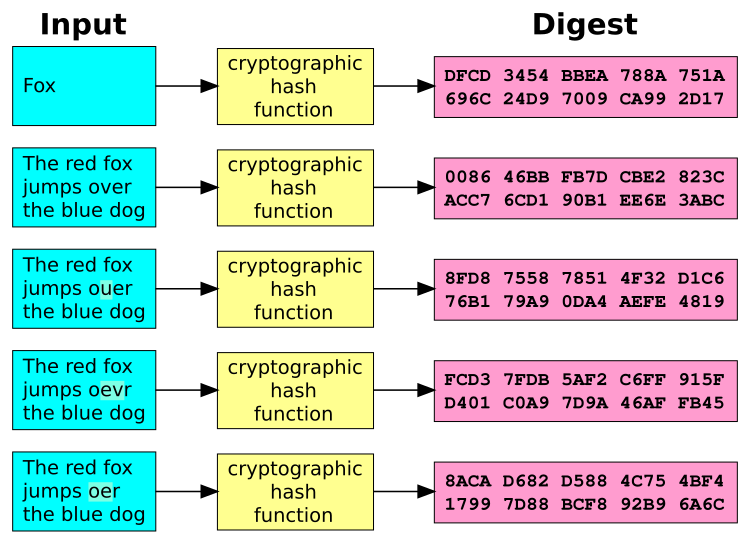
Deterministic output
- Given the same input, a hash function always produces the same output hash value
- Ensures consistency and reliability in hash-based security applications (digital signatures)
- Enables efficient verification of data integrity without requiring the original input data
Fixed-length output
- Cryptographic hash functions produce a fixed-size output regardless of the input size
- Common output sizes include 128 bits (MD5), 160 bits (SHA-1), 256 bits (SHA-256), and 512 bits (SHA-512)
- Fixed-length outputs facilitate efficient storage, comparison, and transmission of hash values
Pre-image resistance
- Given a hash value, it should be computationally infeasible to find an input that produces the same hash value
- Prevents an attacker from determining the original input data from the hash value alone
- Ensures the one-way property of hash functions, making them suitable for password storage and key derivation
Second pre-image resistance
- Given an input and its corresponding hash value, it should be computationally infeasible to find another input that produces the same hash value
- Prevents an attacker from finding a second input that collides with the original input's hash value
- Crucial for maintaining the uniqueness and integrity of hash-based identifiers and digital signatures
Collision resistance
- It should be computationally infeasible to find two different inputs that produce the same hash value
- Collision resistance is a stronger property than second pre-image resistance
- Essential for preventing hash-based security vulnerabilities (hash collisions in digital certificates)
Types of hash functions
MD5
- Message-Digest algorithm 5, developed by Ronald Rivest in 1991
- Produces a 128-bit hash value, typically represented as a 32-character hexadecimal string
- Widely used in the past for data integrity checks and password hashing, but now considered cryptographically broken
SHA-1
- Secure Hash Algorithm 1, developed by the US National Security Agency (NSA) in 1995
- Generates a 160-bit hash value, usually represented as a 40-character hexadecimal string
- Deprecated due to potential vulnerabilities and the emergence of more secure alternatives (SHA-2 family)
SHA-2 family
- Consists of six hash functions: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, and SHA-512/256
- Developed by the NSA in 2001 as a successor to SHA-1, offering improved security and longer hash outputs
- SHA-256 and SHA-512 are widely used in modern security protocols (TLS, SSH) and blockchain technologies (Bitcoin)
SHA-3 family
- Developed through a public competition held by NIST, with the winning algorithm Keccak selected in 2012
- Includes four cryptographic hash functions: SHA3-224, SHA3-256, SHA3-384, and SHA3-512
- Offers a different design approach (sponge construction) and additional security features compared to SHA-2
Applications of hash functions
Data integrity verification
- Hash functions enable efficient verification of data integrity by comparing the computed hash value with the expected value
- Commonly used in file downloads, software updates, and data transmission to detect accidental or malicious modifications
- Examples include MD5 checksums for ISO images and SHA-256 hashes for verifying downloaded files
Password storage
- Hash functions are used to securely store user passwords in databases, avoiding the storage of plaintext passwords
- When a user enters their password, it is hashed and compared with the stored hash value for authentication
- Salting and key stretching techniques (PBKDF2, bcrypt) are employed to enhance password hash security
Digital signatures
- Hash functions are a fundamental component of digital signature schemes (RSA, ECDSA)
- The hash value of the message is signed instead of the entire message, reducing computational overhead
- Digital signatures provide authentication, integrity, and non-repudiation in secure communication and data exchange
Blockchain technology
- Hash functions form the backbone of blockchain technologies, ensuring the integrity and immutability of transaction data
- Each block in a blockchain contains a hash of the previous block, creating a tamper-evident chain of blocks
- Proof-of-work consensus mechanisms (Bitcoin mining) rely on finding a hash value that meets specific criteria
Hash function attacks
Birthday attack
- Exploits the birthday paradox to find hash collisions faster than brute-force methods
- The probability of finding a collision increases significantly with a smaller number of hash values compared to the output space
- Affects hash functions with insufficient collision resistance, such as MD5 and SHA-1
Brute-force attacks
- Involves systematically trying all possible inputs to find a specific hash value or collision
- Feasible for hash functions with small output sizes or weak pre-image resistance
- Mitigated by using hash functions with larger output sizes (SHA-256, SHA-512) and salting techniques
Rainbow table attacks
- Precomputed tables that store hash values and their corresponding inputs to speed up password cracking
- Reduces the time required to find a matching password hash compared to brute-force methods
- Countered by using salting techniques and slower key derivation functions (PBKDF2, scrypt)
Length extension attacks
- Exploits a weakness in the Merkle-Damgård construction used by some hash functions (MD5, SHA-1)
- Allows an attacker to append data to a message and compute a valid hash without knowing the original message
- Mitigated by using hash functions with different construction methods (sponge construction in SHA-3)
Secure hash algorithm design
![Deterministic output, Hash tables explained [step-by-step example] · YourBasic](https://storage.googleapis.com/static.prod.fiveable.me/search-images%2F%22Deterministic_output_in_hash_functions_for_network_security_and_forensics_data_integrity_verification%22-hash-table.png)
Merkle-Damgård construction
- A common design principle used in many hash functions, including MD5, SHA-1, and SHA-2
- Divides the input message into fixed-size blocks and iteratively processes them using a compression function
- Ensures that the hash function is collision-resistant if the underlying compression function is collision-resistant
Sponge construction
- An alternative design approach used in the SHA-3 family of hash functions
- Consists of an absorbing phase, where the input message is absorbed into the state, and a squeezing phase, where the output is generated
- Provides additional security features, such as resistance to length extension attacks and variable output sizes
Compression functions
- A core component of hash function design that takes a fixed-size input and produces a fixed-size output
- Commonly based on block ciphers (AES) or dedicated designs (SHA-2 compression functions)
- Must satisfy certain security properties, such as collision resistance and pre-image resistance, for the overall hash function to be secure
Hash function performance
Computational efficiency
- Hash functions are designed to be computationally efficient, allowing for fast processing of large amounts of data
- Efficiency is crucial for applications that require real-time hash value generation or verification (digital signatures, file integrity checks)
- Achieved through optimized algorithms, lookup tables, and bit-level operations
Hardware acceleration
- Modern processors often include dedicated instructions for accelerating hash function computations (Intel SHA extensions, ARM Cryptography Extensions)
- Hardware acceleration significantly improves the performance of hash-intensive applications (cryptocurrency mining, secure boot)
- Enables faster and more energy-efficient hash value generation compared to software implementations
Parallelization techniques
- Some hash functions, such as the SHA-3 family, are designed to be parallelizable, allowing for concurrent processing of input data
- Parallelization enables faster hash value generation on multi-core processors or distributed systems
- Particularly beneficial for applications that require high-throughput hashing (blockchain mining, large-scale data integrity verification)
Hashing vs encryption
- Hashing and encryption are both cryptographic techniques, but they serve different purposes
- Hashing is a one-way process that generates a fixed-size output (hash value) from an arbitrary-length input, while encryption is a two-way process that converts plaintext into ciphertext using a key
- Hash functions are primarily used for data integrity, authentication, and non-repudiation, while encryption is used for confidentiality and secure communication
- Hashing does not require a key and is irreversible, whereas encryption uses a key and can be reversed (decrypted) with the appropriate key
Future developments in hash functions
Post-quantum cryptographic hash functions
- With the advent of quantum computing, there is a need for hash functions that are resistant to quantum attacks
- Post-quantum cryptographic hash functions are designed to withstand attacks by quantum computers, ensuring long-term security
- Research focuses on hash function constructions based on mathematical problems that are believed to be hard for quantum computers (lattice-based, code-based, multivariate)
Advances in hash function security
- Ongoing research aims to improve the security and efficiency of hash functions
- Development of new hash function designs that offer better resistance to known attacks and improved performance
- Exploration of novel applications of hash functions in emerging technologies (Internet of Things, quantum-resistant digital signatures)
- Standardization efforts by organizations like NIST to provide guidelines and recommendations for secure hash function usage